InfoGuard AG (Headquarter)
Lindenstrasse 10
6340 Baar
Switzerland
InfoGuard AG
Stauffacherstrasse 141
3014 Bern
Switzerland
InfoGuard Deutschland GmbH
Frankfurter Straße 233
63263 Neu-Isenburg
Germany
InfoGuard Deutschland GmbH
Landsberger Straße 302
80687 Munich
Germany
InfoGuard Deutschland GmbH
Am Gierath 20A
40885 Ratingen
Germany
InfoGuard GmbH
Kohlmarkt 8-10
1010 Vienna
Austria
With the IoT, a global computer has been created – but how to keep it under control?
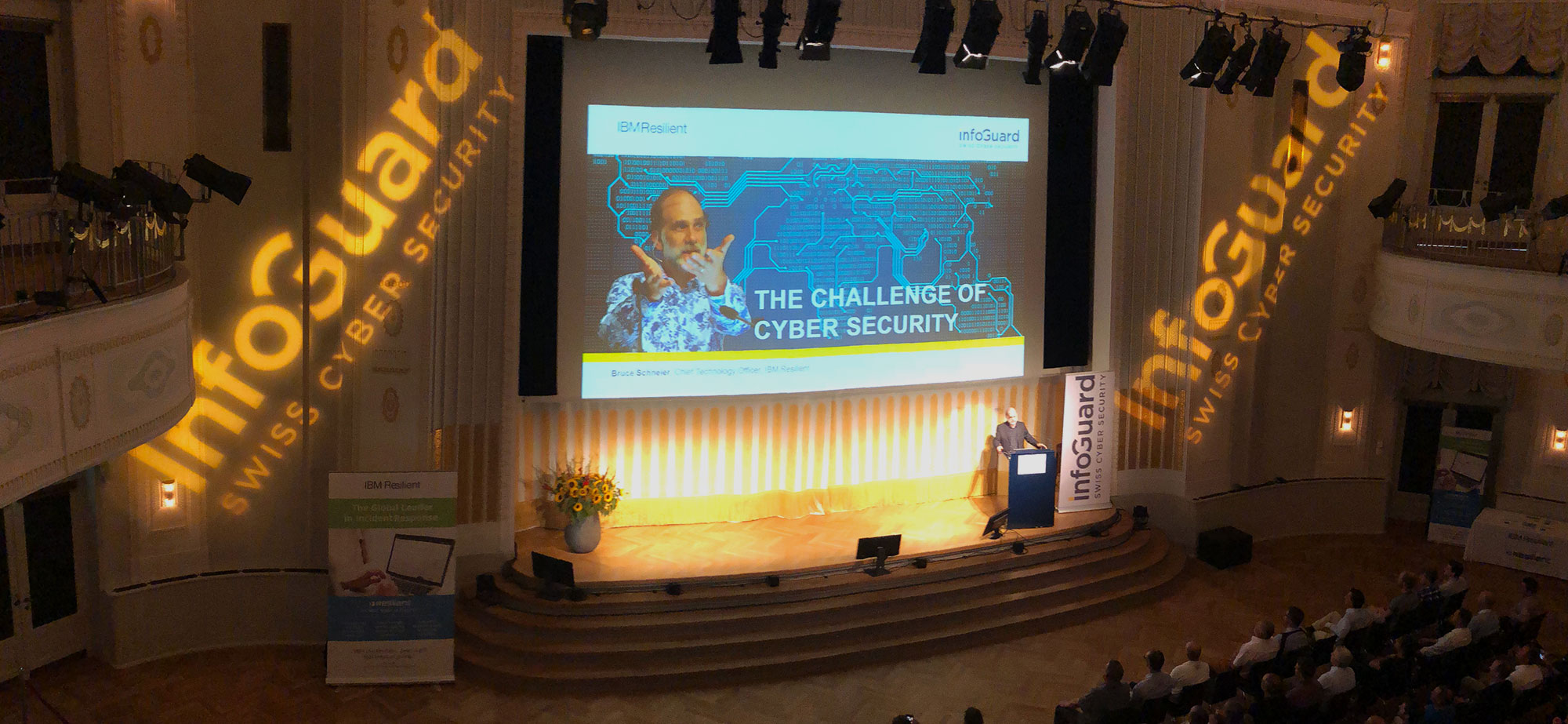
"Click Here to Kill Everybody!" This is the title of the latest book from world-renowned security expert, Bruce Schneier. He explained what it was all about briefly at the InfoGuard talk at the Theater Casino in Zug. There, more than 230 guests were captivated by Bruce Schneier's fascinating presentation of the cyber security challenges to come in the next few years. Did you miss the event? No problem! We sum up the most interesting points for you in this post.
In the increasingly networked and digitalised world, it is vital to detect cyber attacks quickly and respond to them promptly. We demonstrated this at the InfoGuard Talk event at Zug Casino. The undisputed highlight was the presentation by world-renowned computer security and cryptography expert, Bruce Schneier. In his interesting speech, he highlighted the cyber security challenges of today and tomorrow. In so doing, Schneier emphasised that security is notoriously always an arms race between the attacker and the defender, one that is influenced by technology and thus the balance changes – in favour of or, unfortunately, more often, to the disadvantage of the defender.
IoT is a global (insecure) computer
The world's largest computer has been constructed with the Internet of Things. Many years ago, the telephone – perhaps you still remember the black PTT devices on the wall with the coiled cord – was just there for making phone calls. Today, smartphones are powerful computers that can also be used to make phone calls. However, this has long since no longer been the smartphone's primary function! Over the years, "Things" have been turned into "Things" with an embedded computer. Today, it is a computer for multiple "Things".
Why the Internet of Things is so insecure
The question is now: How can this global computer be controlled? To understand this, we have to look at why it is generally insecure. Bruce Schneier listed six main reasons:
- The internet was not built for security: When the internet was developed, security was only taken into consideration with respect to physical attacks on the network. The fault-tolerant architecture can handle failed or faulty servers and connections but not systematic attacks on the underlying protocols. The basic internet protocols were designed without any security considerations. Many of them are even still insecure today.
- Connecting everything together via the internet creates new vulnerabilities: The more we connect things together, the more impact weaknesses in one device will have on others. Moreover, vulnerabilities are everywhere and are particularly difficult to rectify since no one system is actually to blame. Instead, it is the insecure interaction between two individually secure systems.
- Complex systems are difficult to make secure: Nowadays, hackers have an advantage over defenders. One of the main reasons lies in the complexity of the systems. Why? Because more people, parties, errors in the development, interactions, abstraction layers, etc. are involved and there are numerous opportunities to hide weak points in the code.
- The software is badly written and insecure: If the complexity was not enough, we exacerbate the problem by producing poor software. Well-written software is both expensive and time-consuming to create. And who wants that? In most cases, poorly written software will suffice. We would rather live with cheap, buggy software than pay the high price for good software. That is the wrong approach however when taking security seriously.
- Launching a cyber attack is easier than defending against one: There are several reasons for this. The main one being the complexity of the systems, however. Greater complexity means more people involved, more system components, more interactions, more errors in the design and development process, etc. etc. In short: more of everything in which hidden vulnerabilities can lurk. A complex system means more points of attack. The defender must secure all such points of attack. The attacker only needs to find one weak point – an unsecured attack path – and can decide how and when to attack. it is not a fair fight but it is, unfortunately, (cyber) reality.
- Computers can be used for a wide range of applications: Since everything around us is perceived as a computer, this trait of expandability also applies to virtually everything. Each device can be programmed, or even manipulated, to suit any preference. Hackers have proven this by getting a thermostat and a digital camera to play the computer game Doom. Such expandable systems are extremely difficult to secure since it is simply not possible to think through and secure against every configuration, application and dependency. In addition, such systems are not adequately sealed off and are thus designed so they can be expanded with new functions (in other words, software) which then leads back to point 3.
A lack of security in the IoT can end in tragedy
In spite of all these unfavourable prospects, there is a need to protect confidentiality, integrity and availability. A lot of cyber attacks target the first. This involves data theft or data misuse. Of course, some attacks are also aimed at the availability of information or services, such as ransomware and DDoS attacks. For many, however, the confidentiality of information or privacy is the most crucial security objective. But, confidentiality is not everything – especially not in the IoT environment. When a hacker intercepts the communication in my car, it's also not very pleasant. If they also manipulate one of the many control computers in the car however and it results in a tragic or even fatal accident, this is undoubtedly worse for any of us.
The three greatest security challenges of the IoT
Unfortunately, security is always a compromise. It is often a matter of "security versus convenience", "security versus functionality", or even "security versus performance". Computers are also so insecure because we often prioritise convenience, functionality and performance over security. And, even if that were not the case, either way, it is now difficult to effectively implement cyber security, something Bruce also explained in his reasons listed at the start.
In conjunction with the IoT however, another three critical points arise:
- Lack of patching capability: Remember: software always has bugs! Unfortunately, many low-cost solutions do not even offer the ability to install updates. Plainly and simply because the costs of doing so are too high. So, upon becoming aware of a weak point, you have the choice of living with it or getting rid of the device and replacing it with another.
- Authentication is difficult: Knowing precisely who is on the internet is difficult. Authentication is also always a compromise between security and usability – does this sound familiar? You know the cartoon with the two dogs on the computer captioned "On the internet, no one knows you're a dog"? This image* from 1993 illustrates the problem perfectly.
The IoT has not reduced this problem, quite the opposite. Here the authentication does not take place between a person and a device (or service) but, rather, between two devices. The former we can consciously manage, the latter not. As a user, therefore, you have no influence over the devices/services your device connects to. - Supply chain security: Having control over its entire supply chain is a huge challenge. No company today can afford to have all components developed and produced in-house. There is simply not the know-how or time since time-to-market is extremely important (not just for the IoT) in order to gain the competitive edge. And so, each product is always a patchwork of different hardware and software components from various suppliers from different countries. The chance of one of these components having an inbuilt vulnerability is high. It is little wonder then that Bruce Schneier has found weaknesses or even backdoors in a number of components.
In his book, Bruce lists several ways of – as he puts it – making the internet+ more secure. At the InfoGuard Talk, he emphasised one point in particular: when it comes to security within the internet+, the government plays a crucial role. Mandatory requirements are needed and he is convinced that something will be set in motion in the next few years. The EU has already taken the first step in the right direction with the GDPR. In many cases, however, there is still a need to catch up on a political level when it comes to understanding in relation to cyber security – and we, as security experts, are also required to change this. So are the manufacturers as well, however. Best practices, which have already been established in other areas, also need to be applied and implemented for IoT devices – these challenges are certainly not new!
Don't miss the next opportunity
The 230 visitors to the InfoGuard Talk in Zug were impressed and the length of the queue for the subsequent book signing reflected that. We thoroughly recommend the latest book by Bruce Schneier, "Click Here to Kill Everybody"! You will also find a few images from the event over on our website.
Sign up for our newsletter now so you don't miss any of our future events! Not only will you receive information about our upcoming events, but you will also learn about the latest cyber security and cyber defence trends, products and insights.
*(Peter Steiner, "On the Internet, nobody knows you're a dog.", The New Yorker, 5. July 1993)
https://www.newyorker.com/magazine/1993/07/05
https://en.wikipedia.org/wiki/On_the_Internet,_nobody_knows_you%27re_a_dog
Blog

Data Sovereignty in the Cloud: Who else besides you knows about your Data Flows?

Agentic AI: When Autonomous AI Systems Become a Security Risk


