InfoGuard AG (Headquarter)
Lindenstrasse 10
6340 Baar
Switzerland
InfoGuard AG
Stauffacherstrasse 141
3014 Bern
Switzerland
InfoGuard Deutschland GmbH
Frankfurter Straße 233
63263 Neu-Isenburg
Germany
InfoGuard Deutschland GmbH
Landsberger Straße 302
80687 Munich
Germany
InfoGuard Deutschland GmbH
Am Gierath 20A
40885 Ratingen
Germany
InfoGuard GmbH
Kohlmarkt 8-10
1010 Vienna
Austria
How to use Office 365 securely in hybrid environments

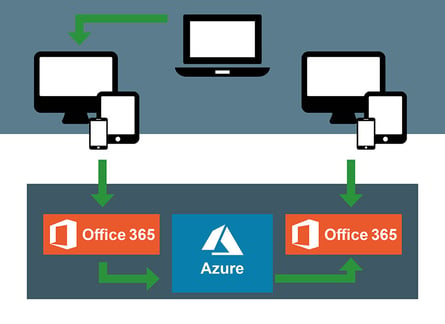
An increasing number of Swiss companies are losing their inhibitions about the cloud and are using services. Quite often it's Microsoft Office 365 – you too? If so, then this comes as no surprise, because the suite makes companies more agile and efficient. But only a few companies use Office 365 purely as a cloud-based solution; instead, they use it in a hybrid environment. In other words, they are also storing data locally. In order to prevent data losses and to be compliant with the GDPR, the "basic" security configuration of Office 365 is not enough. This is why we have put together the most important tips to boost your data security in hybrid environments.
These days, hybrid environments have become widespread. However, many companies are unaware that combining on-premises protection with cloud security is creating extra challenges. This is no easy job, especially when it comes to data and how to handle it, while being sure to remain compliant with the Data Protection Ordinance (GDPR).
Welcome to the dense data jungle
You are probably familiar with this – people are often reluctant to part with data, because, after all, you never know when you might need it at some point in the future... However, storing this data can be risky, particularly if it involves personal data about customers and employees or valuable intellectual property. Unfortunately, Office 365 is also part of the problem.
Most companies are storing sensitive, confidential data both locally (on-premises) and in the cloud(s) – and often they are not even aware of it. As a result, data is in danger of being forgotten about, especially as hybrid environments impose new security requirements and increase the risk of security incidents. This is because there is data flowing between local storage and cloud repositories such as
Office 365.
Our expert tip: Create transparency in your data jungle. We realise though that this is easier said than done. If you would like to find out more about this issue, you can also read one of our other blog posts.
Is Office 365 security inadequate?
Office 365 has many useful built-in security features such as:
- eDiscovery to back up data and perform forensic investigations when needed.
- Exchange Online Protection to filter e-mails for spam and malware.
- Azure Active Directory to manage access rights in the cloud, including appropriate admin accounts and multi-factor authentication.
- Azure Identity Protection to detect suspicious activity and take extra action to minimise risk.
- Data Loss Prevention within Office 365
- Data Encryption during transmission and storage
- Mobile Device Management (MDM)
 As well as these, to complement Exchange Online Protection Microsoft has recently introduced Advanced Threat Protection to provide better protection against zero-day attacks. Office 365 also offers security features that protect against malicious links, along with attachments like Cloud App Security and Threat Intelligence. We have compiled a clear document to show you what this looks like in practice. Download our free security checklist and optimise your Office 365 cloud security right now!
As well as these, to complement Exchange Online Protection Microsoft has recently introduced Advanced Threat Protection to provide better protection against zero-day attacks. Office 365 also offers security features that protect against malicious links, along with attachments like Cloud App Security and Threat Intelligence. We have compiled a clear document to show you what this looks like in practice. Download our free security checklist and optimise your Office 365 cloud security right now!
But don't forget that all these security features are only designed for data within the cloud platform – in other words, cloud providers are not responsible for any locally-stored (on-premises) data or data stored in another cloud. But where data is stored for data security and control should be irrelevant. Only a holistic approach with unified rules and overall controls can provide real security. This is why in hybrid environments, Office 365's built-in security features need to be complemented by additional security measures.
Best practice security strategies for hybrid environments
It is expected that some business-critical applications will remain on-premises for some time to come. This means that in hybrid environments, the security features built into Office 365 must be supplemented in order for maximum security, transparency and effectiveness to be achieved. Some of the relevant security features are CASB and UEBA, which will be described in greater detail below.
Before you can add features, your biggest risks need to be identified, prioritised and minimised – before incidents occur. It doesn't matter whether the data is available locally (on-premises) or in Office 365. In addition, your security needs to be geared to who is accessing your data on-premises or in the cloud. The only way to ensure that the right people have the right Access to Data (IAM is key) is by ensuring end-to-end transparency. To do this, you should use a privilege model based on minimum rights assignment. It is crucial to include data owners in the authorisation check process.
As a rule, this role is assigned to a person from the specialist departments or project groups. Part of the job is also taking responsibility for and confirming access rights. This way, the data owners know exactly who needs what access and who currently holds it. It also saves time to automate authorisation checks and workflows, as well as reducing effort and assisting you in making the right access control decisions.
From the point of view of best practice, as well as the General Data Protection Regulation and other legal regulations, you need to be familiar with all files containing sensitive and personal information. They need to be classified to effectively protect data and comply with compliance requirements. The classification must be applied both in hybrid environments and in your local data storage. It is therefore advisable to automate this process, making sure that all storage locations are included.
CASB and UEBA ‒ sensible security measures to take in hybrid environments
For example, Cloud Access Security Brokers (CASB) help prevent the unauthorised use of critical cloud services (loss of IP, vulnerabilities, weak encryption, data location, etc.), as well as blocking access to unauthorised cloud applications as well as blocking access to unauthorised cloud applications (Shadow IT) and protecting data from unauthorised disclosure.
Many cloud service providers provide basic (static) threat modelling; however, some native tools lack a detailed context about user behaviour. For example, they cannot detect when accounts are exhibiting suspicious behaviour on-premises.
Hence, many integrated tools are no substitute for dynamic, behaviour-based threat analysis and detection. You can increase security and reduce false positives with advanced User and Entity Behaviour Analytics (UEBA) which is also designed for hybrid environments.
Security in hybrid environments is complex ‒ make use of our experience!
Even proof of compliance can be difficult in a hybrid cloud environment. Not only must you ensure that on-premises and, for example, Office 365, Cloud AWS, and other solutions are compliant, but you must also ensure that your cloud environment is compliant. It also needs to be demonstrated that dynamic cloud usage, service networking, management and cloud resource orchestration, among other things, is assured and secure. Therefore multi-cloud environments require an approach to security that is platform-independent and standardised. Take advantage of the experience and competence of our cyber security experts. We will support you, not only in terms of design and architecture but also in implementing additional security measures and in targeted testing of your hybrid environment, e.g. using targeted penetration tests. Please contact us. We will work together to optimise your cloud strategy
Hybrid cloud environments have huge potential and you should be taking advantage of this potential. But you shouldn't just rely on the integrated security functions of the cloud provider, because they definitely don't go far enough!
Blog

Cyber Threat Intelligence: Risikoexpositionen erkennen, bevor Angreifer es tun

Daten-Souveränität in der Cloud: Wer ausser Ihnen kennt Ihre Datenflüsse noch?



