InfoGuard AG (Headquarter)
Lindenstrasse 10
6340 Baar
Switzerland
InfoGuard AG
Stauffacherstrasse 141
3014 Bern
Switzerland
InfoGuard Deutschland GmbH
Frankfurter Straße 233
63263 Neu-Isenburg
Germany
InfoGuard Deutschland GmbH
Landsberger Straße 302
80687 Munich
Germany
InfoGuard Deutschland GmbH
Am Gierath 20A
40885 Ratingen
Germany
InfoGuard GmbH
Kohlmarkt 8-10
1010 Vienna
Austria
Phishing – why responsiveness is just as important as prevention

Going phishing on our clients' behalf – and what you can learn from it
For me and my colleagues, phishing campaigns are part of our daily lives – of course, we are working as "good hackers". Using phishing campaigns, we test our customers' preventive and reactive protective measures – both in technical and social terms.
Most of the phishing campaigns we carry out have a success rate of well over 10%, which is (unfortunately) a very good result for a hacker. In addition, we notice again and again...
- …only a very small number of employees (if any) notify their security department (Security Operations Center team) about the phishing attack.
- …employees who have been successfully attacked delete the phishing mail as soon as they detect the attack. In this scenario, too, the SOC team often remains uninformed about the incident.
- …the SOC team does not respond to an incident in an appropriate manner, for example by blocking access to the phishing website via web proxy.
- …after becoming aware internally of the phishing attack, the SOC team’s recommendations are not complied with by the employees, e.g. by changing their passwords, deleting phishing e-mails, etc.
A nanosecond of time with massive consequences
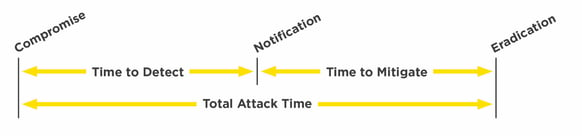
This failure to act needlessly extends the time between the initial exposure ("time to detect") and the detection of the attack. As a result, cyber criminals have more time to dig deep into the IT infrastructure, and to hide. This, of course, extends the time between containing the attack and cleaning it up ("time to mitigate") – or even in extreme cases makes it impossible. The attacker rejoices in the time they are given. The SOC team and management are not very happy at all...
4 immediate measures to be taken in the event of successful phishing attacks
Now that you have grasped the subject and, most importantly, the problem, we will deal with point two, reactive measures if, despite taking preventive measures, the worst case scenario occurs.
Reactive actions also need to be taught in awareness training. After all, the more and more professional attacks there are, the higher the probability that phishing e-mails will fail to be identified as such – despite raising awareness. Employees need to know what to do in the event of a successful phishing attack and what to avoid. We have summarised the four most important points for you below:
- Provide your employees with specific recommendations for taking action, for example in the form of a checklist, and tell them how to reach the SOC team (preferably around the clock). Together with your SOC team, create the checklist, based on which they can then take over the case. They are the best placed to know what information they need.
- Ensure clear internal communication by stating that instructions from the SOC team, such as changing passwords, must be implemented immediately and with no exceptions.
- Many employees do not behave incorrectly when a successful phishing attack happens, because they are afraid of punitive actions. For this reason, awareness training should also address the psychological aspects. Make it clear to your employees that there should not fear any personal consequences – quite the opposite. By reacting rapidly, they are actively contributing to the company's security.
- Finally, security awareness and so the way people react to a successful phishing attack should be subjected to regular testing. On one hand, this ensure employees' security awareness and, on the other hand, the SOC team can rehearse the emergency and, in doing so, make improvements to processes.
Professional Security Awareness is worthwhile
In practice, we see over and over again that many companies know – in theory – that it is important to be aware of security. Nevertheless, very few of them have implemented appropriate measures or even conducted awareness training. We are not the only ones who believe that phishing will become increasingly significant in the future, and that targeted awareness is one of the key factors in effective cyber security. The statistics also prove it again and again (unfortunately). That's why you should rely on a professional partner with extensive expertise and experience.
Our InfoGuard specialists can draw on many years of practical experience in the field of security awareness. Our 360° approach means we know almost every trap you and your employees can fall into. We can offer you targeted employee awareness training for the safety and risk-conscious handling of information in daily business. Interested? Get in touch with us – my colleagues and I look forward to making your business more secure!
By the way, creating awareness is the be-all and end-all of
preventing successful attacks. We have created a poster for you
so that you and your employees can familiarise yourselves with
the most important rules concerning phishing e-mails.
Don't give phishing e-mails a chance, and expose cyber criminals before the worst comes to the worst – download now for free!
Blog

Cyber Threat Intelligence: Risikoexpositionen erkennen, bevor Angreifer es tun

Daten-Souveränität in der Cloud: Wer ausser Ihnen kennt Ihre Datenflüsse noch?


