InfoGuard AG (Headquarter)
Lindenstrasse 10
6340 Baar
Switzerland
InfoGuard AG
Stauffacherstrasse 141
3014 Bern
Switzerland
InfoGuard Deutschland GmbH
Frankfurter Straße 233
63263 Neu-Isenburg
Germany
InfoGuard Deutschland GmbH
Landsberger Straße 302
80687 Munich
Germany
InfoGuard Deutschland GmbH
Am Gierath 20A
40885 Ratingen
Germany
InfoGuard GmbH
Kohlmarkt 8-10
1010 Vienna
Austria
Two-factor authentication - when double security is cut in half

For a long time now, it has been obsolete to use just username and password as sole access protection. When it comes to accessing online services, two-factor authentication (2FA) is standard these days. But be careful, as 2FA is vulnerable too, as the examples of Vovox and Reddit proved not so long ago. This article explains what you need to bear in mind when using two-factor authentication.
Millions of text messages - including SMS with codes for two-factor authentication – are openly available in the network
In November 2018, Techcrunch magazine reported that a database containing a total of 26 million text messages was hosted on the unprotected server belonging to an American service provider. According to its own advertising, the California-based company delivers texts in 180 countries. With Elasticsearch from Amazon and the Kibana frontend also running on the server, anyone could search the database for names, phone numbers and even the content that had been transmitted.
Examining the database revealed some very explosive content, such as a password from the Chinese dating provider Badoo to a customer, as well as numerous 2FA codes from Google accounts providing access to the internal systems of large corporations. In addition, there were numerous messages used by services to validate customer identities. Disclosing this data could have had serious consequences.
The data had been entered into the open database in almost real time, so attackers could have read messages even before a user had had the opportunity to use the authentication code, or they could have carried out the authentication themselves. According to the provider, this security gap was closed immediately, but this is not an isolated case!
Even the Reddit hack shows the limits of 2FA via text messaging
In summer 2018, Reddit made public a major security incident. Hackers were able to access a variety of systems and copy current email addresses and a database backup. The attack was carried out using an intercepted access code for the text-based 2FA that had been set up. SMS-based 2FA is significantly less secure than the use of 2FA solutions based on hardware tokens or a dedicated app (see NIST SP 800-63). What this can mean in connection with the GDPR has been covered extensively in earlier blog articles.
The two incidents clearly show that the seemingly double security can become single security in one fell swoop!
Two-factor authentication: Yes, of course - but how should it be done?
Please don't misunderstand us. We also strongly recommend the use of 2FA – but done the right way! Every correct authentication factor poses an additional hurdle for attackers, hence an extra protection factor for you. However, as has been seen, the use of SMS 2FA is not necessarily the ultimate benchmark. All too easily, access codes may be intercepted and misused by attackers.
FIDO is revolutionising 2FA authentication
The Fast Identity Online Alliance (FIDO) has developed an open framework that will revolutionise online authentication. The standards should make "simple, fast and secure" internet authentication a reality. The personal data and private keys always remain exclusively in the user's possession and are not stored on public servers. There are three basic factors that can be freely combined for authentication purposes:
- The user's knowledge, e.g. passwords or PIN
- A possession belonging to the user, e.g. a security token according to the U2F standard
- A user characteristic, e.g. fingerprint, voice or facial appearance
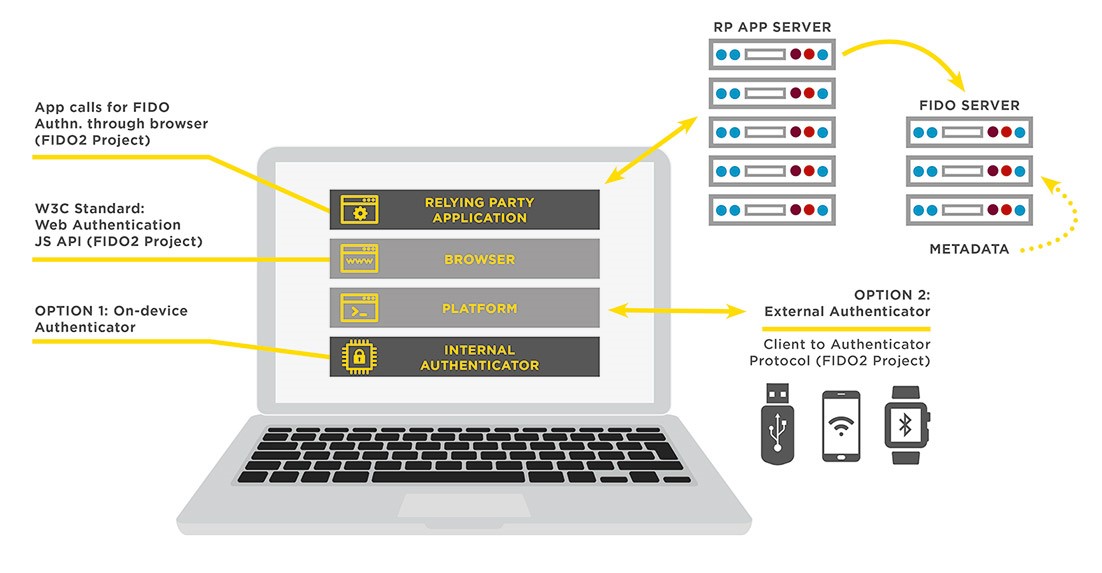
Figure 1: Source fidoalliance.org
Want to implement such an open, scalable and interoperable approach to FIDO authentication? Watch the video below to learn more. Our partner OneSpan will show you how you can integrate FIDO face recognition, fingerprint or other biometric authentication methods to provide users with a fresh - and above all secure - authentication experience for mobile and online services.
Would you like to know more? Then download our free whitepaper. It will tell you everything you need to know about the EU Authentication and Transactions Directive, as well as how FIDO is revolutionising online authentication - concisely in ten pages!
Blog

InfoGuard Threat Intelligence Report Q2/26: Europas Cyberrisiko, Salt Typhoon & Irans Rückkehr
NIS2-Leitfaden für Schweizer Anbieter: So gelingt die Umsetzung!



