InfoGuard AG (Headquarter)
Lindenstrasse 10
6340 Baar
Switzerland
InfoGuard AG
Stauffacherstrasse 141
3014 Bern
Switzerland
InfoGuard Deutschland GmbH
Frankfurter Straße 233
63263 Neu-Isenburg
Germany
InfoGuard Deutschland GmbH
Landsberger Straße 302
80687 Munich
Germany
InfoGuard Deutschland GmbH
Am Gierath 20A
40885 Ratingen
Germany
InfoGuard GmbH
Kohlmarkt 8-10
1010 Vienna
Austria
Security
Consulting

Security Consulting
Cyber Security
Strategy
Cyber Risk Resilience
ISO/IEC 27001 | Information Security Management System (ISMS)
Do you want to be sure that your cyber security is built on a solid and reliable long-term foundation and can also be quickly and easily adapted to future requirements? Our experts support you in formulating a long-term security strategy or in setting up a flexible framework for the structured management and targeted minimisation of all ICT risks. A cyber security framework (Information Security Management System) not only helps you to better manage your internal risks, the structured framework also greatly simplifies the implementation of compliance and risk management requirements.
Our ISMS/DSMS services include:
- Establishment and further development of an information security management system (ISMS) in accordance with ISO 27001
- CISO-as-a-Service / Security Officer Services
- DPC-as-a-Service / Data Protection Coordinator
- Development of a sustainable security strategy
- Support with (re-)certification in accordance with ISO 27001
- Auditing your organization os your ISMS in accordance with ISO 27001
- Development of security policy, guidelines / policy, guidelines / procedures & guidelines
- Definition of the security organization, functions and their task descriptions
- ISMS and ICT-Security-Management-Tool
Cyber Security Framework (NIST)
Do you want to be sure that your cyber security is built on a solid and reliable long-term foundation and can also be quickly and easily adapted to future requirements? Our experts support you in formulating a long-term security strategy or in setting up a flexible framework for the structured management and targeted minimisation of all ICT risks. An NIST-based cyber security framework not only helps you to better manage your internal risks, the structured framework the implementation of compliance and risk management requirements.
We advise and support you on the following topics:
- CISO as a Service / Security Officer Service
- Development of a sustainable security strategy
- Risk analyses pursuant to ISO 27005
- NIST CSF Gap-Analysis
- Development of security policy, guidelines / policy, guidelines / procedures & guidelines
- Definition of the security organization, functions and their task descriptions
ICT Security Management
.
Incident Response Planning | Crisis Management
Tabletop Exercises (TTX)
With our Table-Top Exercises (TTX), we review the existing cyber security & recovery processes together with you and your team on the basis of formulated scenarios. These scenarios deal with the strategic crisis organisation and/or the IT operational level. The focus is on building organisational and operational skills (crisis organisation, communication, reporting obligations in the event of cyber and data protection incidents, recovery, etc.) through the scenario-based simulation of crisis situations.
- Table-top exercises / simulation for the crisis management team
- Table-top exercises / simulation for the technical IT emergency organization
- Management workshop to process the security incident and recover the ability to act
Business Continuity Management (BCM)
Governance, Risk
& Compliance
CISO-as-a-Service
DPC-as-a-Service
IT, Cloud & Security Governance
Cyber-Third Party Risk Management (C-TPRM)
Drawing on our many years of experience in the field of cyber security, we support you in establishing and further developing a structured Cyber Third Party Risk Management (C-TPRM) framework. A systematic C-TPRM provides transparency regarding your third parties, reduces cyber risks throughout the supply chain and ensures compliance with regulatory requirements. The approach builds on existing concepts such as Cyber Supply Chain Risk Management (C-SCRM) and develops them further in a targeted manner.
Our services cover the entire C-TPRM lifecycle:
- Conceptual C-TPRM: Establishment of a structured framework with clear processes, governance and methodologies – for transparency, standardisation and compliance.
- Supplier assessment: Classification and evaluation of your third parties, identification of risks and derivation of concrete measures – for informed decisions and effective management.
- TPRM-as-a-Service: Support with the establishment, further development or operational management of your C-TPRM – flexible, efficient and with direct access to experienced specialists.
Data Protection (CH revDSG / GDPR)
At first glance, digitalisation and data protection are difficult to reconcile. However, successful digitalisation requires the inclusion of data protection and is therefore a strategically important issue – for every company. The data protection experts at InfoGuard support you across the board when it comes to these issues: from questions relating to data protection requirements, analysis, strategy definition and conception to sensitisation and implementation.
Our data protection services include:
- Gap analysis of the Swiss Data Protection Act (CH revDSG) and the European General Data Protection Regulation (GDPR)
- GDPR web application audit on the Internet and webshops (disclaimer, cookies, data processing etc.)
- Sensitisation of employees to data protection
- Data protection strategy development pursuant to national data protection legislation (DSG) and GDPR
- Data protection impact assessment (DPIA)
- Certification support
- DPC-as-a-Service to support the DPO
- Data protection management system (tool)
- Auditing of external data processors
Compliance Management (NIS2, DORA, CRA, FINMA, SWIFT, PCI DSS, SIC)
Compliance requirements such as ICS, CH revDSG, EU GDPR, NIS2, CRA, DORA, FINMA, SWIFT, PCI DSS or SIC are constantly changing and becoming ever more extensive. InfoGuard helps you to optimally implement and efficiently operate the various compliance requirements. We advise you on the applicable requirements. We also support you in analysing and implementing security measures in accordance with the relevant specifications. This ensures that the legal requirements are consistently complied with and correctly implemented on an ongoing basis.
We advise and support you on the following topics:
- CISO as a Service / Security Officer Service
- DPC as a Service / Data Protection Coordinator
- Carrying out a gap analysis with regard to the applicable requirements
- Implementation of systematic compliance management
- Support through an appropriate information security management tool (ISMS)
Certification Guidance (ISO 27001, ISO 27701, TISAX, IEC 62443, CMMC)
Do you want to improve your cyber security by setting up an information security management system (ISMS) in accordance with ISO 27001 or optimise your existing ISMS? Our experienced and certified auditors will accompany you on the way to ISO 27001, ISO 27701, TISAX, IEC 62443, CMMC certification.
We advise and support you on the following topics:
- Development and introduction of an Management System in accordance with ISO 27001, ISO 27701, TISAX, IEC 62443
- (Re-)certification pursuant to ISO 27001, ISO 27701, TISAX, IEC 62443, CMMC
- Further development of your ISMS in accordance with ISO 27001
- Auditing your ISMS in accordance with ISO 27001
Security Architecture
& Design
Network & Security Architecture | Zero Trust
We help you to set up an appropriate network and security architecture. Based on the ISO 27001 standard, we identify the missing elements in a gap analysis and highlight the associated risks. An action plan is then drawn up as a basis for operational implementation and prioritised according to risk. This ensures that you’ll be able to react quickly to new requirements in the future and put optimal IT security measures in place.
We advise and support you on the following topics:
- Definition of an IT security architecture in accordance with international standards (ISO, NIST and BSI)
- Determination of protection requirements through systematic risk analysis
- Support in maintaining all business processes
- Integration of IT security as an integral part of the IT architecture
Microsoft Azure, AWS, GCP, Cloud Security Governance
The demands on cloud security governance are growing ever faster. In an age of Azure, AWS, GCP and many other cloud services, managing information and data correctly is essential, but also complex. There is often a lack of a holistic approach to guaranteeing the availability, confidentiality, integrity and traceability of information and data. Our cloud governance service ensures that the provision of resources, system integration, data security and other aspects of cloud computing is properly planned, considered and managed. InfoGuard helps you to optimally implement and efficiently operate the various requirements.
- Cloud risk assessment
- Defining and ensuring systematic cyber supply chain risk management
- Data protection impact assessment (DPIA)
IoT | Industry 4.0 | OT | Smart Infrastructure
Modern information and communication technologies are networking the industrial world. Operational technology (OT) is of great interest to cyber criminals because the increasing automation of industrial processes requires OT and IT technologies to be networked, which is changing the threat and risk landscape. Your OT infrastructures are also business-critical. Our services enable you to identify potential vulnerabilities in your IoT, OT, Industry 4.0 or smart infrastructure at an early stage and initiate appropriate protective measures.
Our experienced OT specialists help you to verify the key components, set up the architecture in line with the defence-in-depth approach, implement security in accordance with IEC 62443, establish suitable supplier risk management and thus contribute significantly to reducing security risks.
Our OT security services at a glance:
- Asset recognition – visibility of operating technology
- Evaluation of the threat landscape
- Evaluation of the protection concept
- Holistic assessment of “defence-in-depth” system security
PAM | IAM
By using cloud services and personal devices (BYOD), users can access data from anywhere. As a result, access management (privileged access management PAM and identity & access management IAM) has shifted from a perimeter-based to an identity-centred approach. As such, identity governance & administration becomes a key function and a prerequisite for strategic security objectives such as:
- Privileged Access Management
- Identity & Access Management
- Zero Trust security model
- Need-to-Know principle
- (Data Protection &) Security by Design
- (Data Protection &) Security by Default
With our 360° view and our business-to-identity services, we support your endeavours from planning and operation through to compliance. Our process model enables effective and sustainable implementation of identity governance & administration. Success factors are a high level of automation and integration. We accompany you on the way to viable PAM & IAM solutions that are impressive in legal, technical and organisational terms.
Human-Centered
Security
Awareness Concept for Awareness-as-a-Service
Awareness Campaign
Social Engineering Simulation
Awareness Trainings: Management Workshop | Awareness Show | Security Arena
Phishing Simulation
Awareness Platform | Web-Based Training | E-Learning
Cyber Security
Assessments
Your business processes only work if the right information is always available in the right place at the right time. Confidentiality, integrity and availability of information play an important role here. Our independent and tailored cyber security assessments and cloud security assessments will show you which organisational, technical, personnel and legal vulnerabilities exist in your company and which improvement measures are expedient.
As part of our security analyses, our experienced and certified experts review your concepts, procedures, infrastructure, processes and organisational structures in accordance with various international security and industry guidelines. This gives you the certainty that the defined objectives are achieved in accordance with best practice and that undesirable events are prevented. The answers as to whether the existing measures are sensible and appropriate complete the safety checks.
Analysis on the CH revDSG & GDPR
Swift (Society for Worldwide Interbank Financial Telecommunication) Assessment
Year after year, Swift tightens up the regulations for financial service providers. Not only are new Swift controls added, but Advisory is upgraded to Mandatory. And a problem for many companies is the one-year period within which the adjustments have to be made. What’s your situation? Our Swift assessment provides clarity.
“2025 Swift Provider – Customer Security Programme Assessment”: Benefit from our expertise and many years of experience. Our staff includes Swift Certified Assessors in the subject area: CSP Assessments. Read more about certification here.

Microsoft Azure, AWS, GCP , Cloud Security Governance
Microsoft 365 Security Assessment
Phishing Simulation
Social Engineering Audit
Incident Response Readiness Assessment
Managed Detection &
Response (MDR)
Extended Detection & Response (XDR)
Extended Detection & Response (XDR)
Do you have any questions about our Security Consulting Services?
Cyber Defence & Incident Response
Cyberangriffe erkennen, abwehren und Handlungsfähigkeit wiederherstellenIm InfoGuard Cyber Defence Center (CDC) in der Schweiz arbeiten über 80 hochqualifizierte Cyber Security Expert*innen und Analysten. Das CDC an unserem Standort in Baar ist ISO 27001 zertifiziert und ISAE 3000 Typ 2 überprüft. Es verfügt über ein mehrstufiges, physisches Sicherheitskonzept und die Sicherheitssysteme werden rund um die Uhr überwacht. Die vitalen, technischen Komponenten sind mehrfach ausgelegt und garantieren höchste Verfügbarkeit. Gleichzeitig erfüllen wir die strengen Vorgaben des Datenschutzes (DSG und EU DSGVO/GDPR) und die Richtlinien für den schweizerischen Finanzsektor.
Zudem wird sichergestellt, dass die Daten ausschliesslich beim Kunden oder in unseren redundanten Rechenzentren in der Schweiz gespeichert werden. InfoGuard ist BSI-qualifizierter APT-Response-Dienstleister, Mitglied bei FIRST (Global Forum of Incident Response and Security Teams) und agiert zudem als Incident Response-Partner und Schadensabwickler von führenden Versicherungen, Brokern und Schadensabwicklern, was den hohen Qualitätsstandard der Cyber Defence und Response Services unterstreicht.
Zudem wird sichergestellt, dass die Daten ausschliesslich beim Kunden oder in unseren redundanten Rechenzentren in der Schweiz gespeichert werden. InfoGuard ist BSI-qualifizierter APT-Response-Dienstleister, Mitglied bei FIRST (Global Forum of Incident Response and Security Teams) und agiert zudem als Incident Response-Partner und Schadensabwickler von führenden Versicherungen, Brokern und Schadensabwicklern, was den hohen Qualitätsstandard der Cyber Defence und Response Services unterstreicht.
Bei all unseren Kunden mit einem MDR-Service konnten wir erfolgreich einen Business Impact durch Cyberangriffe verhindern.
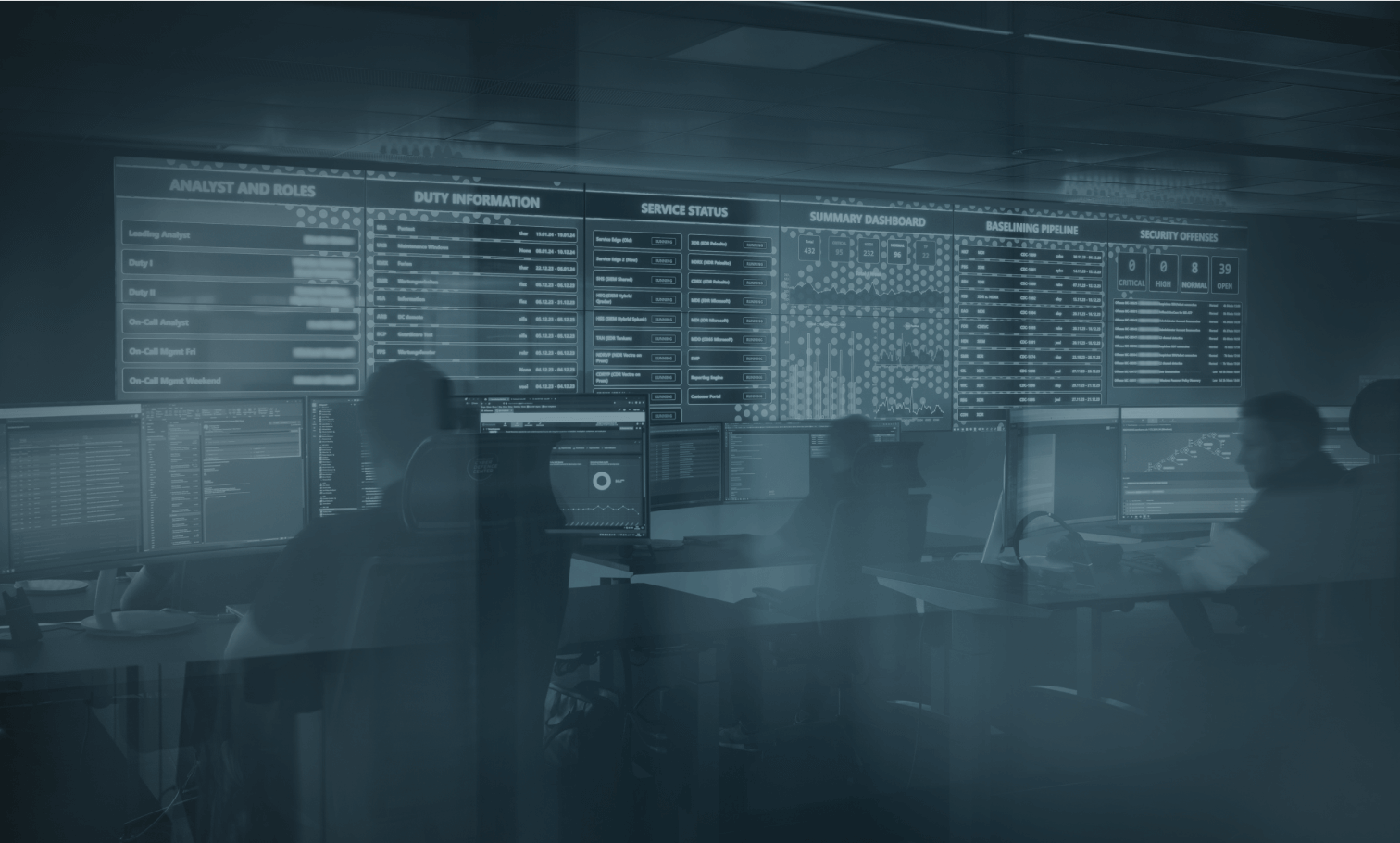
Profitieren Sie von unserer langjährigen Erfahrung
24/7
Managed Detection & Response Services aus unserem CDC in der Schweiz
80+
Experten in dedizierten SOC-, CSIRT- und Threat-Intelligence-Teams
12+
Jahre SOC-Erfahrung & Kompetenz
300+
Cyber Defence- & CSIRT-Kunden
4
Wochen für das strukturierte SOC-Onboarding
Hunderte
Incident-Response-Fälle
pro Jahr
BSI-qualifizierter APT-
Response-Dienstleister &
FIRST-Mitglied
Swiss
SOC-Plattform
Cyber Defence Platform
InfoGuard Cyber Defence Plattform
Herzstück einer wirksamenund effektiven Cyber Defence
Die eigenentwickelte, hochskalierbare und On-Prem in der Schweiz betriebene InfoGuard Cyber Defence Platform bildet das Kernstück unserer Cyber Defence Services und basiert auf einer offenen XDR-Architektur.
Um sicherzustellen, dass wir Bedrohungen aus allen Blickwinkeln sehen, sammelt die Plattform Daten von Endgeräten, Netzwerken, IoT-/OT-Infrastrukturen, Cloudumgebungen und Identitäten.
Durch die Nutzung unterschiedlicher Erkennungsmethoden, einschliesslich Machine Learning, kann die Plattform schnell Anomalien und verdächtige Verhaltensweisen aufdecken und mit Erkenntnissen aus aktuellen Sicherheitsvorfällen, simulierten Cyberattacken und Threat-Intelligence-Feeds anreichern, um unsere Analystenteams zu unterstützen. Dank der Schwarmintelligenz von Hunderten Kunden, täglich Tausenden von Sicherheitsereignissen und hunderten IR-Fällen ist der bestmögliche Schutz und die schnellstmögliche Reaktion garantiert.
Durch die Nutzung unterschiedlicher Erkennungsmethoden, einschliesslich Machine Learning, kann die Plattform schnell Anomalien und verdächtige Verhaltensweisen aufdecken und mit Erkenntnissen aus aktuellen Sicherheitsvorfällen, simulierten Cyberattacken und Threat-Intelligence-Feeds anreichern, um unsere Analystenteams zu unterstützen. Dank der Schwarmintelligenz von Hunderten Kunden, täglich Tausenden von Sicherheitsereignissen und hunderten IR-Fällen ist der bestmögliche Schutz und die schnellstmögliche Reaktion garantiert.
Die Plattform bietet umfassende Transparenz und arbeitet nahtlos mit Ihrem bestehenden Technologie-Stack zusammen. Dies minimiert das Onboarding und eliminiert die Herstellerabhängigkeit. Zudem ist sichergestellt, dass sensitive Kundendaten jederzeit geschützt sind und ausschliesslich in unserem Data Center in der Schweiz gespeichert werden.
Related Content: Security Consulting



